By Jeff Spann, SVP Information Security Consultant/Regional Director - SBS CyberSecurity, LLC
Board of Directors Responsibilities
Financial institutions are economic engines that drive our communities. At the head of each financial institution is a Board of Directors, who oversee and provide direction for the institution to ensure the operation and meet its customer needs. The responsibility for such oversight is massive and has evolved greatly over the last 10 years to include investments in technology and cybersecurity. The Board is held accountable to the institution’s shareholders, employees, depositors, the community they serve, and the regulators for the operations of an efficient, safe and sound institution.
Each institution is examined and measured on the capital, asset quality, management, earnings, liquidity and sensitivity to market risk, which is known as the CAMELS rating. An institution’s Information Security Program (ISP) is measured in the management component of the CAMELS rating and, when managed proactively, provides safe and sound risk management practices for the operations of the institution.
Managing the ISP is a team effort and includes all operational areas of the institution. To establish an organization that proactively manages the ISP, the Board annually appoints an Information Security Officer (ISO) to oversee the day activities involved in maintaining a well-managed ISP. Though the Board is ultimately held responsible for the ISP, the ISO oversees day-to-day information security activities and reports to the Board at least annually on the overall status of the ISP. Additionally, the Board appoints an Information Technology (IT – or similarly named) Committee to oversee the day-to-day IT operations and information security risk management. The Board reviews and offers credible challenges to IT Committee minutes and reports provided, and as oversight, provides an acceptance or approval.
Much of proactive management is delegated to the ISO and the IT Committee; however, the Board sets the organizational culture regarding security (mindset) and provides the direction for investing in technology and protecting that investment. The Board ultimately determines, intentionally or unintentionally, whether an institution has a reactive or a proactive cybersecurity mindset.
Reactive Mindset versus Proactive Mindset
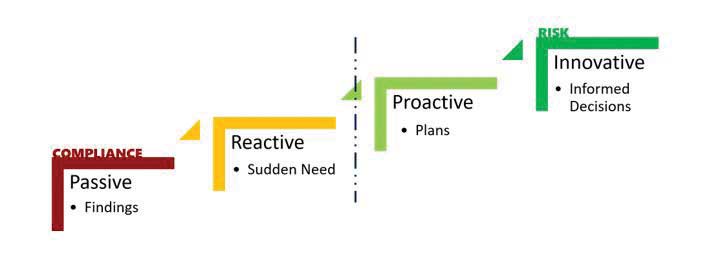
Each institution chooses – knowingly or unknowingly – to take a stance when it comes to its cybersecurity mindset. The different types of mindsets, typically driven by a “sudden need,” include:
- Passive: taking the compliance-driven approach by choosing only to meet regulatory standards, which does not offer protection from today’s cyber threats.
- Reactive: a step beyond passive, but only to include reacting to findings and recommendations from IT exams and audits, which can provide some additional protection, but not enough to prevent or properly respond to a cyber incident.
- Proactive: strategic thinking that moves beyond basic compliance to understand today’s threats and build an ISP that can get out in front of today’s cyber threats and still meet regulatory compliance.
- Innovative: using IT and information security risk assessments to make better, more-informed decisions that can quantify risk and deploy the right controls to mitigate the most risk of a cyber incident.
Shifting from a reactive mindset to a proactive mindset is one of the key decisions a Board of Directors can make to protect the investments made in technology and an institution’s confidential information.
Results of a Reactive Mindset
When a Board continues to have a reactive mindset, the institution will lack good risk management practices, feel frustrated, and may respond to events without proper preparation, which can result in losing control of spending and costing more to recover from a cyber incident than necessary. The mindset is revealed when an audit or exam results in a long list of items not meeting regulatory guidance or industry-standard risk management practices. A reactive mindset can also reveal itself when a cybersecurity incident takes the institution out of operation for extended periods of time with significant financial impacts. The environment becomes inefficient, and the costs of managing the institution reactively become a guessing game.
Benefits of a Proactive Mindset
An institution with a proactive mindset strives not only to achieve a high rating for the management component of the CAMELS rating, but also to do whatever needs to be done to protect the investments it has made. The Board’s responsibility for oversight of the ISP is better managed proactively. Proactive management does not wait for an audit or exam to tell the institution what needs to be done. The proactive mindset takes control and regularly risk assesses all areas of the ISP to act and mitigate the identified risks before threats are realized.
There are many strategic advantages to managing the ISP with a proactive mindset, and some are easy to recognize. At the same time, some are intangible and not as easily recognized until there is reflection. The mindset to be proactive reveals itself in the results of an audit, exam, a cybersecurity incident or a disaster recovery event. A proactive mindset provides a member of the Board and senior management with clarity to handle situations. It allows for better sleep at night, knowing the institution has proactively identified and planned for information security risks.
The Board of Directors Sets the Culture
The Board chooses to have a culture of a proactive mindset or stay in a reactive mindset. A proactive mindset will reduce financial losses, have more efficient processes, gain control of the challenges to the institution, and gain a competitive advantage over the competition.
Here are four questions to ask yourself to help determine your cybersecurity mindset:
- Are we discussing cybersecurity as a Board regularly and growing in our ability to be a “credible challenge” to cybersecurity-related decisions (proactive), or are we just waiting to get through the minimum necessary cyber discussions so we can get back to “real business” (reactive)?
- Are we measuring cybersecurity risk and using the results of our risk assessments to make more informed cybersecurity decisions (proactive), or are we checking the box when it comes to ISP-related risk assessments (reactive)?
- Do we know what our most important IT assets, vendors and business processes are, as well as the top threats to our institution right now (proactive), or are we just reviewing the results of those risk assessments and moving along (reactive)?
- Have we made the proper investments (people, resources, training, and/or money) when it comes to protecting our investments and confidential information (proactive), or do we still treat IT and cybersecurity as an expense (reactive)?
Jeff Spann, SVP Information Security Consultant/Regional Director – SBS CyberSecurity, LLC
For more information, contact Reece Simpson at 605-270-3916 or reece.simpson@sbscyber.com. SBS delivers unique, turnkey cybersecurity solutions tailored to each client’s needs, including risk management, consulting, on-site and virtual auditing, network security and education. Learn more at www.sbscyber.com.
This story appears in 2020-2021 Issue 4 of the Nebraska Banker Magazine






